Видео с ютуба Secure Ai Deployment

AI Security Made Easy

Securing AI Systems: Protecting Data, Models, & Usage

Securing AI Foundry Agent Part 1 (Network Perspective)

Introduction to Cisco Secure AI Factory (CSAIF)

Secure AI Deployment for Businesses

Deploying an end-to-end secure AI application | BRK234

Securing AI deployments - Module 1

AWS re:Invent 2025 - Securing AI Agent Ecosystems: MCP Server & Agent Security at Scale (ISV325)

Securing AI with Azure AI Foundry | Built-in protections for Cloud & AI platforms

How to Secure AI Business Models

Risks of Agentic AI: What You Need to Know About Autonomous AI

What Are Best Practices For Secure AI Deployment?

How to secure your AI environment with Azure Essentials

Security & AI Governance: Reducing Risks in AI Systems

How do you deploy generative AI safely

AI Agents for Cybersecurity: Enhancing Automation & Threat Detection

Secure AI Deployment Strategies 2025 Protect Your Models from IDE Leaks, API Abuse & other Risks
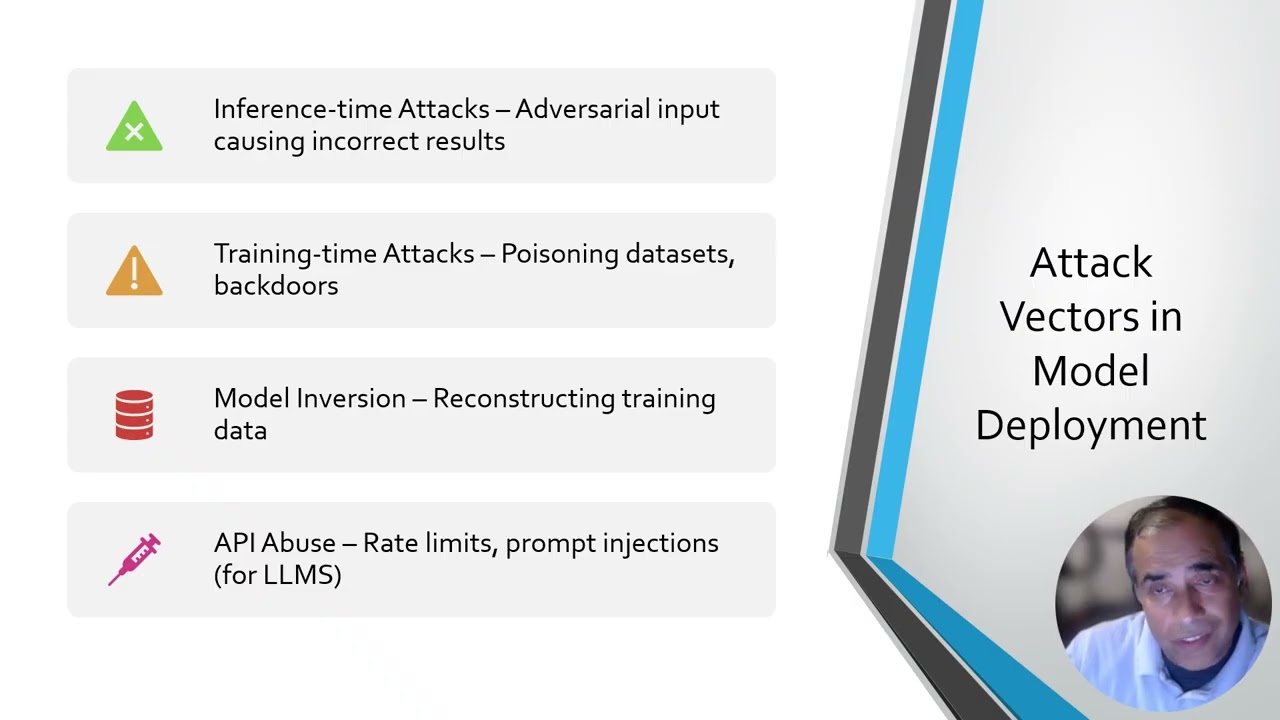
AWS re:Invent 2025 - Advanced AI Security: Architecting Defense-in-Depth for AI Workloads (SEC410)

161 | Secure AI Model Deployment: Model Security Vs Commercialization | Navigating AI Hype

Data security with AI powered agents

LLM Hacking Defense: Strategies for Secure AI

I Deployed a Secure Multi-User AI Agent in n8n

Secure AI Model Deployment

AWS re:Invent 2025 - Secure AI Agents Delivering Efficiency in Regulated Industries (WPS317)
Secure AI Model Deployment